Riding my mountain bike down a huge rock
An illegal trail named Bong Drop in Aliso Woods. This feature is tough cause it is practically vertical at the bottom, and your rolling down a steep slippery, bumpy rock. Recorded by my MTB mentor and Local Legend Paul Tata.
Navenu Update

Being apart of the Navenu project has been amazing. The project has some incredible talented and successful people involved, and I have learned a lot working with everyone. Like any start-up theres points where we are just barely hanging on, and sacrifices must be made. But after everything I feel like we finally made it to an important milestone. The completion of our mobile application for android and IOS. We just wrapped up development and now preparing for a soft launch in London. This was also the first mobile application project I have ever developed, so I am so humbled that everyone in the company put so much faith in me knowing that I did not have any expierence developing mobile applications.
The company is headed in an exciting direction, as we begin our move into the Web3 space. We have also begun applying artificial intelligence into the application.
Top 1% of Strava’s 100+ Million Users for 2022 and more
In 2022 I wound up in top 1% of stravas 100+ Million Users for total amount of activities!

Here are my 2022 Stats.




In 2022 I started mountain biking more. Specifically down hill e-mtb. There are very steep challenging trails right across the street from where i live, and I have made some good friends that are also neighbors that have been teaching me.

I started out this year with a 2020 Haibike

Then bought a Norco Range VLT 900W from my e-mtb mentor Paul Tata, which has pretty much everything you could want on a bike.

See how i roll….On my 2 day adventure

Longest Ride 184 Miles
Flying Down The Canyon
One of my most favorite things to do on a bicycle is coming down Laguna Canyon Road with the Saturday group. There is an amazing synergy, its a PR every time for sure. This particular Saturday is special as our group encountered another group, so it was on like donkey kong. I jumped up in to the front early on but there was a long snake of cyclist behind me. Good times!

Rotating Pacelines on PCH POV
Some footage of the group I ride with on Saturdays. This was a 68 Mile ride from Tustin to Queen Mary Long Beach and back to Tustin. The group dropped
A POV video of us practicing the rotating paceline, I often like to refer to this as “collaboartive cycling”, it is the fastest and most efficient way for a group of cyclist to travel. There are 2 line the left line, the left line is the fast lane, while the line on the right is the slow (recovery) lane. This is only effective and possible with a group of cyclist with similar levels of fitness. We are traveling just under 30 mphs.
Below is quick video of us cycling along the long beach bike path.
New Bike….Still Pedaling….Will hit 10k for 2021
Still cycling, when i started I avoided hills at all cost, but that has changed. I guess I was forced to, cause i moved on top of a very big hill. It is amazing though how each hill gets a little easier and a lot less painful with each climb. La Plata is like 3 big rolling hills here in San Clemente, I didn’t even think La Plata was even possible for me, and after the first time, I vowed to never try it again, just from the pain and agony it caused me. I have been the local legend (most ridden in 90 days) on strava for a while now, I now ride La Plata a couple times a week, and enjoy it. I am also proud of climbing to top of the world in Laguna Beach, probably one of the most challenging climbs around here.
I also picked up a few new bikes, hahaha. 2 Electric Mountain Bikes (HaiBikes) and my favorite a 2020 Trek Emonda SLR.
I am also fortunate and by pure luck came across an epic group of riders, and look forward to riding with them every Saturday, more correctly stated I try myu hardest to keep up with them. They have all been riding togther for a really long time, and they all ride as often and as passionately as i do, and I’m so fortunate that they are willing to let me tag along and teach me the ropes. Like the rotating pacelines, which you rarely see groups of cyclist doing cause it requires everyone in the group to be of the same fitness level, I often refer to it as collaborative cycling.
Ive also driven out to check out some of the crits around CA. Ive pedaled pretty much all of SOuthern California coast.
Just under 14,000 miles since i started cycling just under a year and a half ago. Still love it, and will continue to do so.
Month of May behind bars (not the jail kind)
Surprisingly its been 6 months since i started road cycling, and I literally spent the month of May behind bars. In the process i learned how to wrench the bike including tuning (indexing) the gears and I can fix a flat like a pro with my bare hands. I also got my bike dialed in by swapping out the wahoo bolt for the newer ROAM, upgraded my drive train to the ultegra R8000, and added the garmin RTL-510 rear radar and taillight, and some 60″ carbon fiber rims. The most effective upgrade i made happened to be the cheapiest, and that was switching from rubber inner tube to latex innertubes, it made my bike noticebly faster, and worth having to pump tires before every ride.

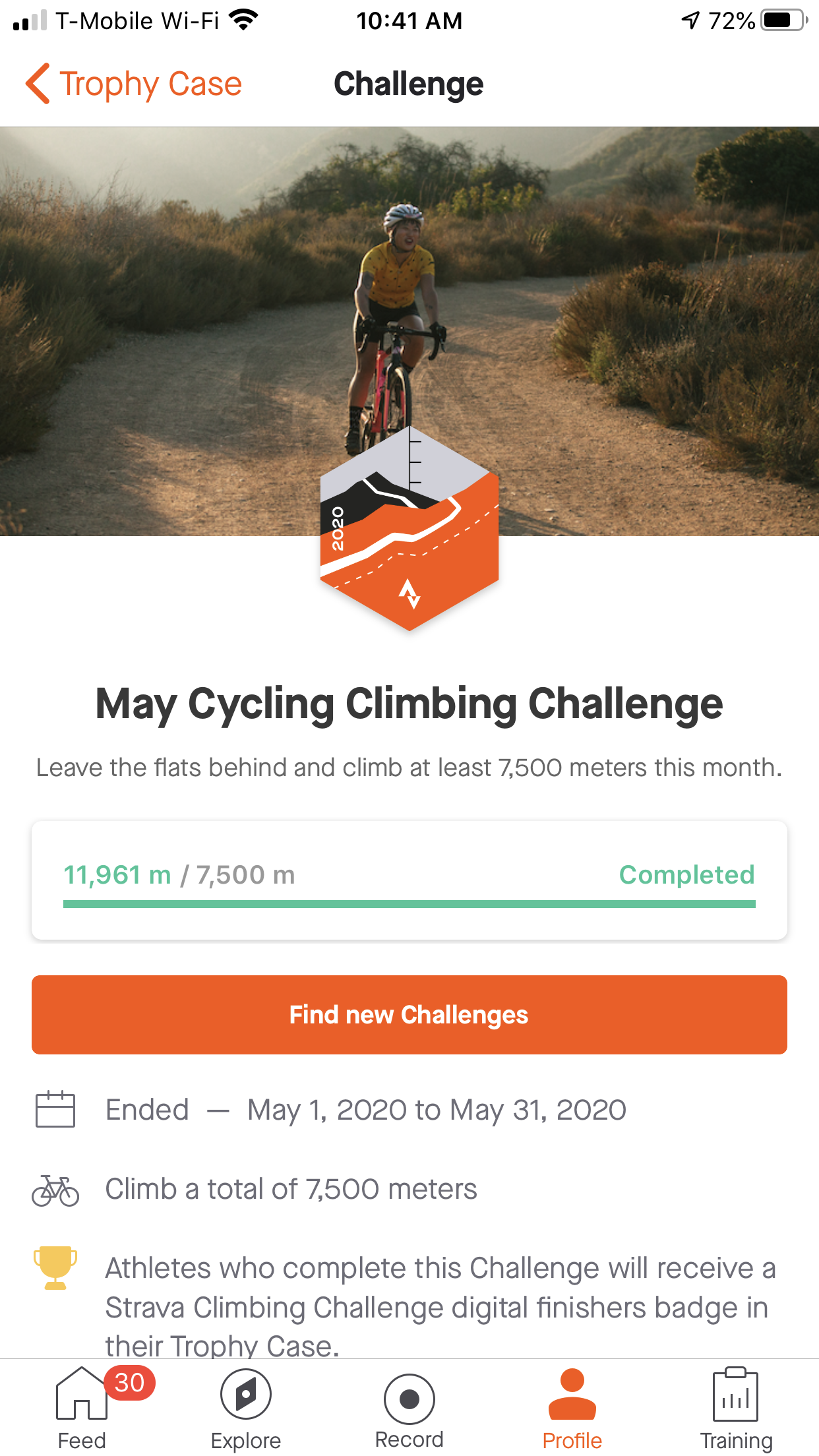
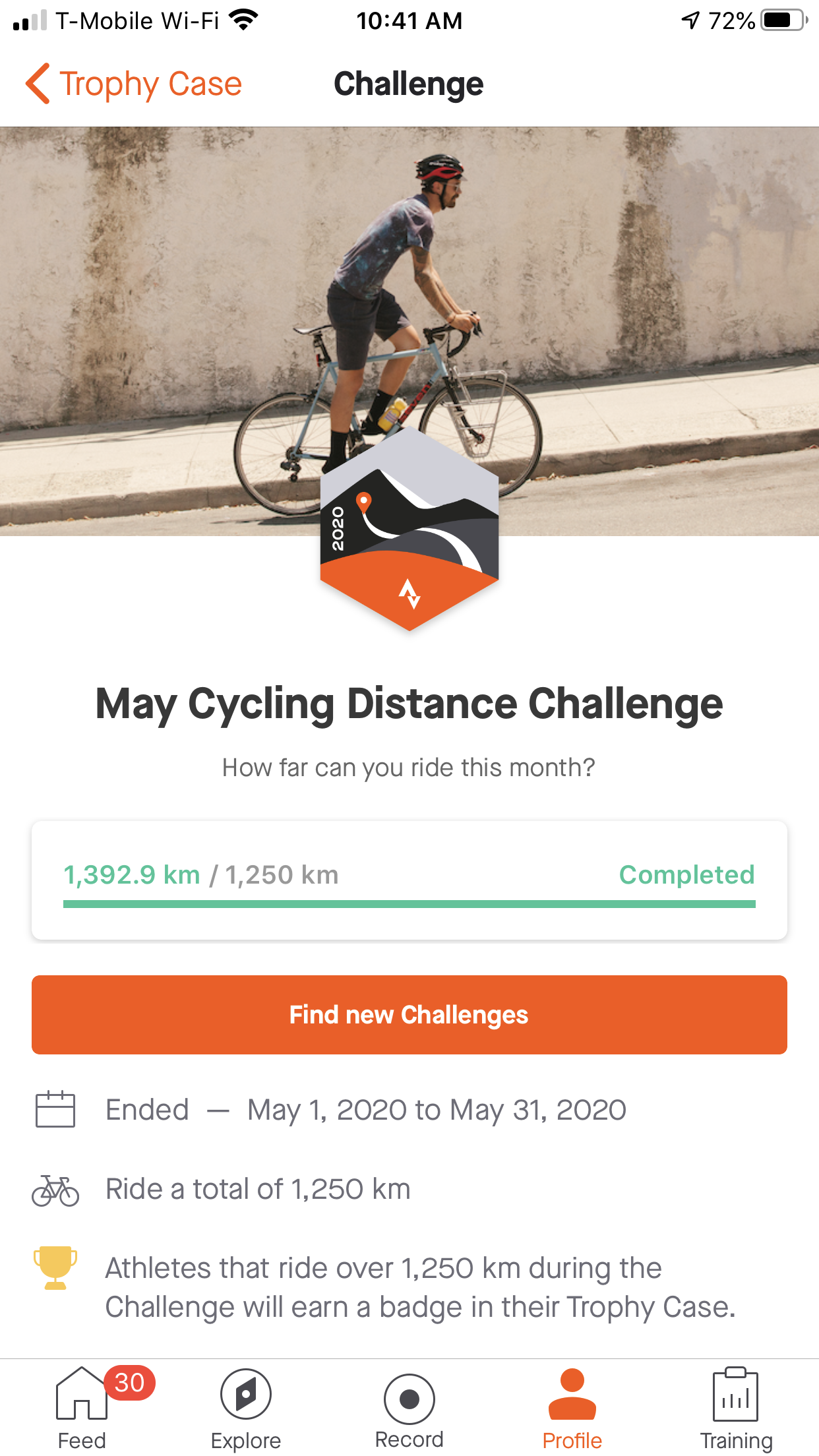
Starting out my goal was to accomplish Strava’s distance and climbing challenges, it took 6 months and i finally was able to accomplish that along with every strava cycling challenge that month. Its currently June and I will do it again ahead of schedule
Strava recently just started “local legends” for which i am currently a legend of 4 segments
My 89 Mile Solo Cycling Journey during COVID lockdown
Tracking OC COVID-19 progression per city
The pandemic has ended thank god! Unfortunately the data is no longer avaliable so i can longer provide a live example but here is a screen shot of what the program looked like.

Thanks to the current pandemic lock down, I have even more extra time on my hands. So i wrote a program that collects the OC gov's COVID data per city, so i can play with the data and maybe see which cities to avoid...Originally when i started Irvine and Newport Beach had the most cases, but then Anaheim quickly jumped to the the top in a few days alongside Irvine (as of april 7th). Southern cities have had minimal cases.
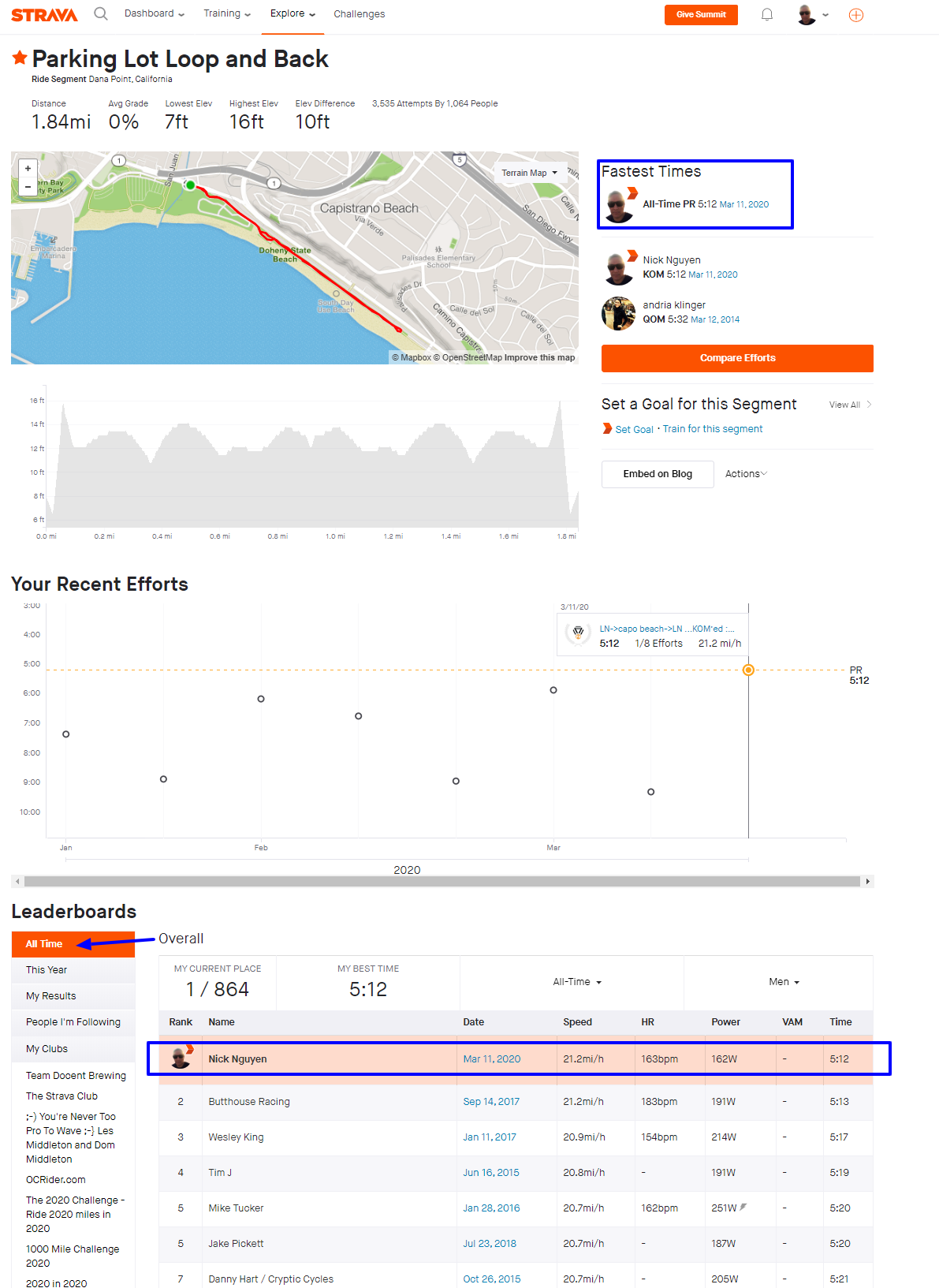
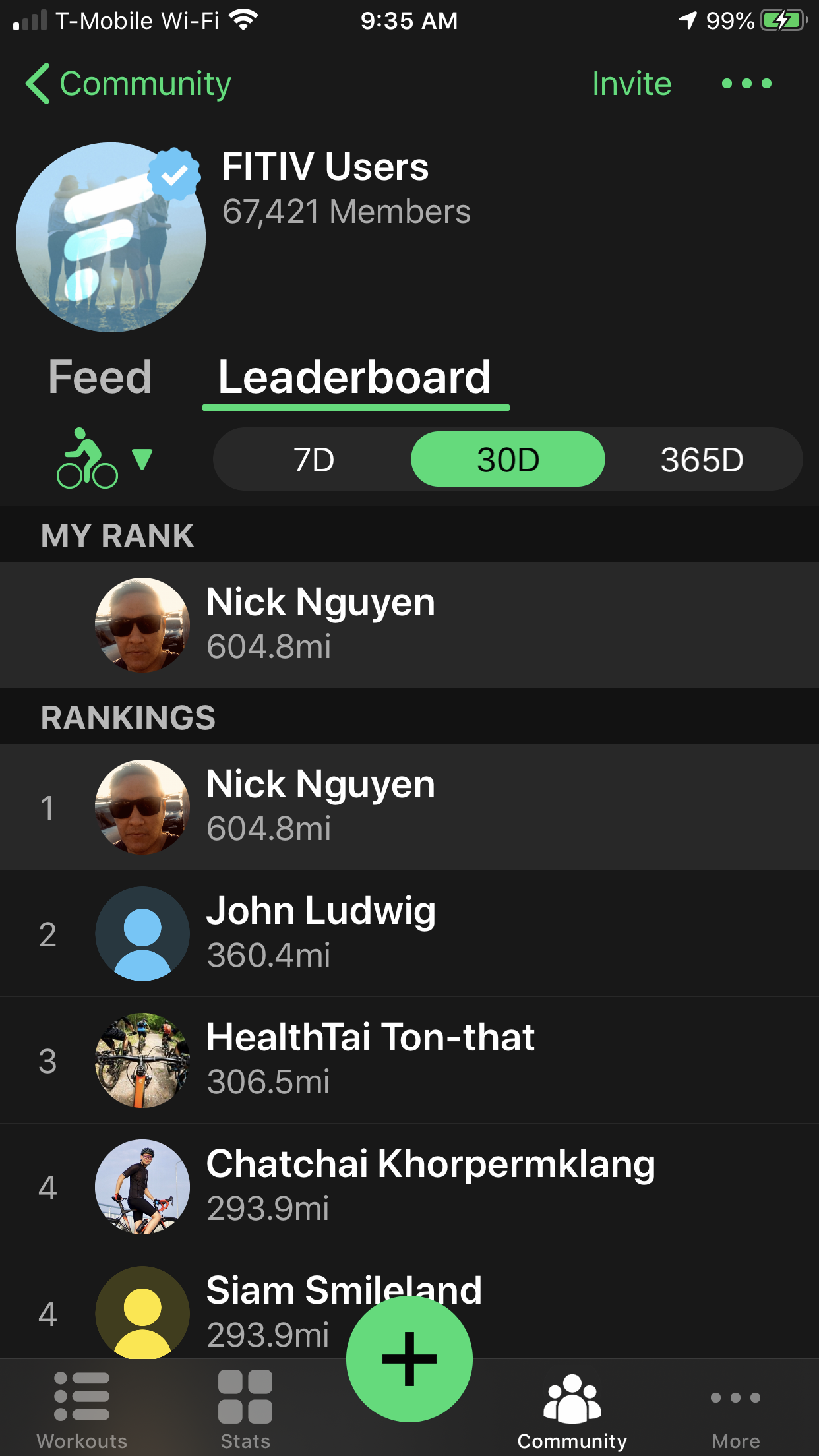
KOM’ed on Strava, Holding #1 on FITIV, and Update on Progression
Aliso Creek Trail loop
See my beautiful regular cycling route
For anyone following the COVID-19 aka coronavirus
My 2 best rides for 2019
So i started cycling in december and managed to put in 300 miles in my first month. something i never even thought was possible. What helped keep me engage was the strava app as it appeals to my competitive spirit, and using the latest technology to monitor and measure my biofeedback, learning about all the health variables and watching there progression over time also helped keep me motivated, most fasinating was learning about the heart rate variable and all that it entails. so in 2019 i completed lofty rides that i never thought was even possible for myself.
laguna niguel to oceanside
riding for 9 miles on the freeway was interesting to say the least.

laguna niguel to newport beach
great network of bike trails from irvine all the way to newport, i plan to do a “there and back” trip this month some time.

i plan to cycle the entire southern california coast from the north end of LA to San diego in the month of january. i also entered the january strava challenge 1250 km in one month. i am currently on track to get the trophy on it.
My latest hobby
Thanks to one my best friends for hooking me up with this mechanical masterpiece.

This trek domane is made of carbon fiber so its light as a feather, and like riding a bullet.

My goal is to ride from Laguna Niguel to Oceanside, and then take a train back, its just about a 40 mile ride, which is a lot for my out of shape ass. but do-able. So in preparation I’ve been training a couple times a week doing a beautiful 12 mile ride from my house in Laguna Niguel to the house my family is building in San Clemente, meanwhile learning about all the technology on the bike and how it applies to my own physical stats.





Powering the tiniest stepper motor
Getting this micro bipolar stepper motor to do what I want was probably one of the hardest things Ive ever had to learn.
These inexpensive stepper motors are from china and there isnt much documentation and I couldnt find any existing code to base off of. So i had to tackle this on my own. Hadd to learn about steps per revolution, PWM, drivers, etc.
Anyways I wound up running L2938 H Driver powered by attiny85 micro controller unfortunately the torque on these motors didnt wind up sufficing for our project, but now I can control just about any stepper motor in the future which im sure will be useful at some point.
Building my perfect motorcycle
Took me 2 weeks to build this from the ground up, this would be my 4th motorcycle, my last one had been stolen and raped before police recovered it, 2 blown motors and one accident on the freeway. Making it kind of sketchy to ride.
So i took the parts off my old bike that i knew were good and then put together this bike, and shes perfect.
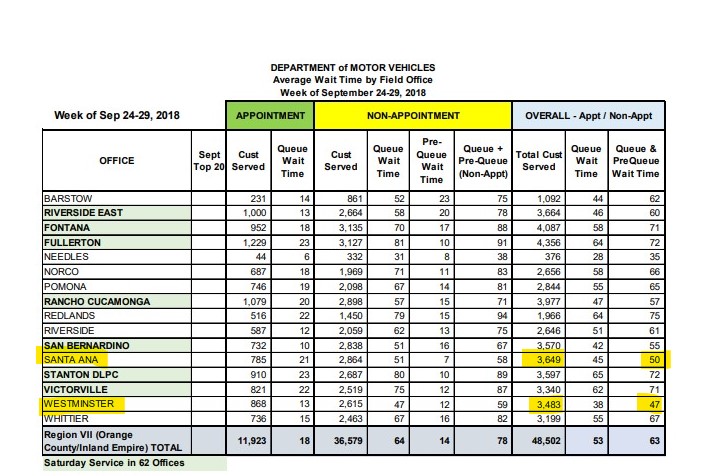
Tracking DMV wait times
So I was required to visit one of our favorite state agencies, the DMV. Its been a while, and when i showed up the line was wrapping around the building. So i went home to spare my day, and figure out a better way to accomplish this civic duty.
With some general knowledge of the existing public data, I attempted to track the wait times for all my local DMV's. and figure out where and when a good time to go to the DMV would be.
Going to the DMV website I found some interesting stats
This data provides a general overview but not the specifics im looking for. After a little more digging I wass able to find "some what" real time wait time on the DMW website: So i proceeded to scrape those wait times into a MYSQL database every 15 minutes for each location. Making use of that much data can be difficult, so i need to make a way to visualize the data, so i employed google charts. If your interested in seeing the ongoing results of this project click here
So i proceeded to scrape those wait times into a MYSQL database every 15 minutes for each location. Making use of that much data can be difficult, so i need to make a way to visualize the data, so i employed google charts. If your interested in seeing the ongoing results of this project click here
 I was able to figure out the best time and location, which i will publish online after I finish my dealings with the DMV. So be sure to check back or subscribe to my site for an update.
I was able to figure out the best time and location, which i will publish online after I finish my dealings with the DMV. So be sure to check back or subscribe to my site for an update.